NIST IAL2
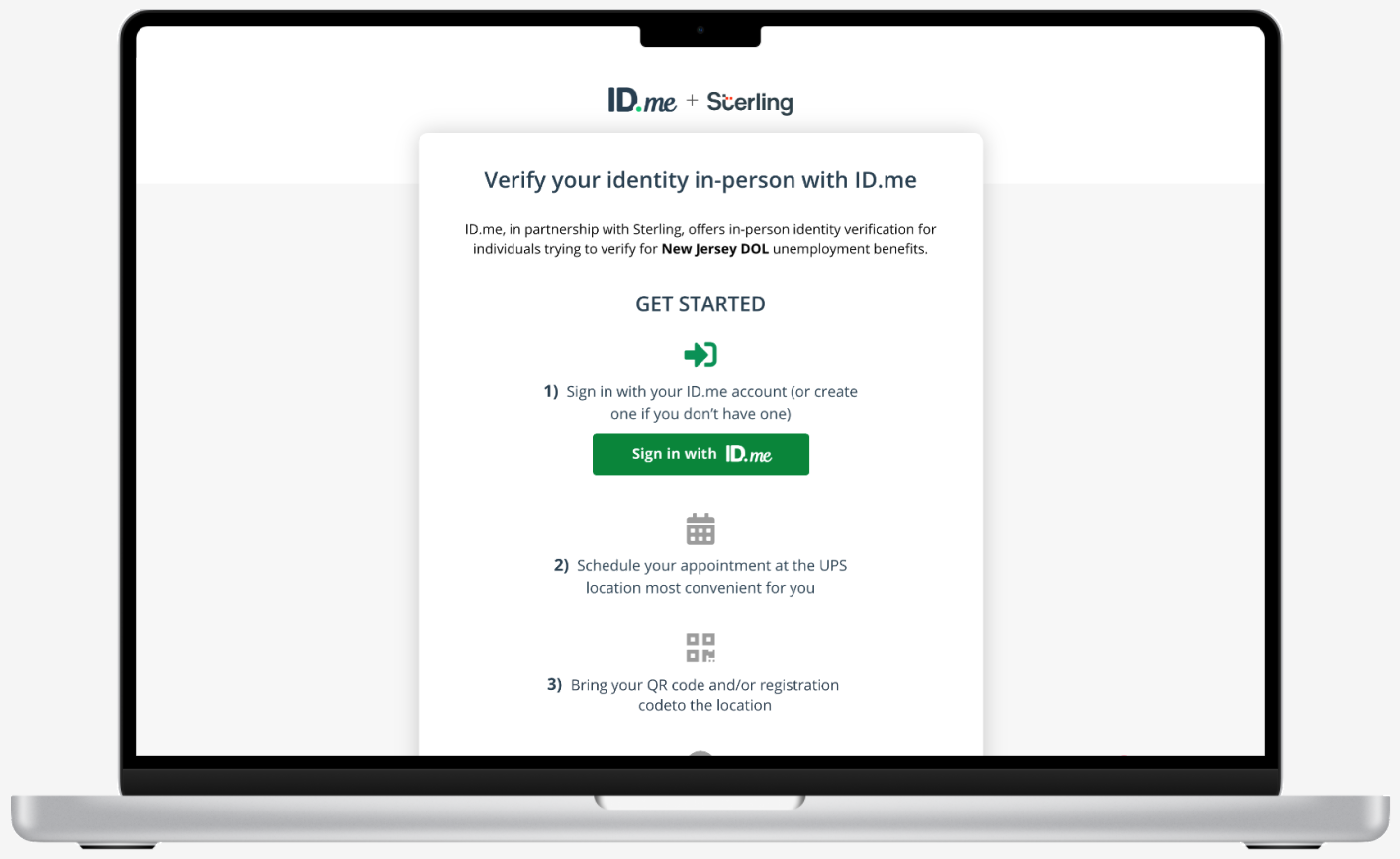
Today, ID.me has nearly 50 million pre-verified users verified at NIST IAL2 and our network is growing by thousands daily. ID.me’s IAL2 solution is omni-channel, featuring expedited preverified, online self-service (Unsupervised Remote), video chat (Supervised Remote), and In-Person (IPV) flows. The Unsupervised Remote workflow is fully automated, and this is how 85% of new users choose to verify their identity, typically doing so in a median of 5 minutes. The remaining are routed through the Supervised Remote workflow to complete verification with an ID.me trained video chat agent (Trusted Referee), or choose to verify in person at one of more than 700 locations across the US.
When to use this policy
IAL2 is ideal to increase user adoption, decrease false negatives, and detect fraudulent identities by a malicious applicants.
Lastly, this policy has the option to join a video call to interact with an ID.me Trusted Referee to complete verification via Virtual Proofing.
Verification is different than KBA and FI in that it follows NIST digital identity standards. NIST IAL2 limits KBA methods and replaces them with devices and biometrics. This policy introduces the need for either remote or physically-present identity proofing.
Who is eligible?
Anyone 18-years or older is eligible to be verified leveraging ID.me’s NIST IAL2 verification solution.
Essence of policy
- One piece of STRONG evidence if the evidence’s issuing source, during its identity proofing event, confirmed the claimed identity by collecting two or more forms STRONG evidence and the CSP validates the evidence directly with the issuing source
OR
- Two pieces of STRONG evidence
OR
- One piece of STRONG evidence plus two pieces of FAIR evidence
Verification flows
Today, ID.me has nearly 50 million pre-verified users verified at NIST IAL2 and our network is growing by thousands daily. Since ID.me takes a network approach, these pre-verified users can now securely access offers, benefits, and services in seconds with just 3-clicks. New users complete verification in a frictionless and convenient manner, using the least amount of information required to verify their identity.
Here you can find what the NIST IAL2 verification user experience looks like today:



Use cases
Here you can find example ID.me use cases: